Hyperscale Cloud
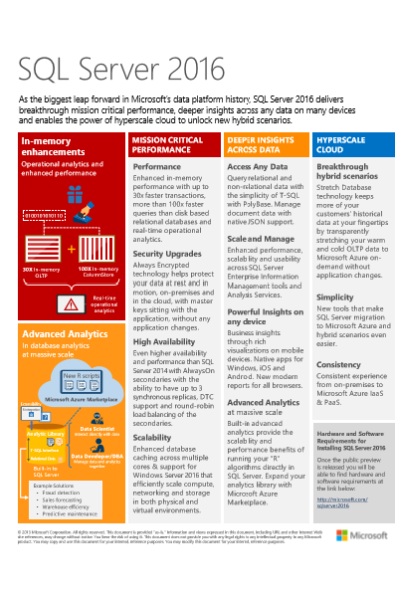
SQL server can deploy a private cloud, hybrid cloud, public cloud and can use familiar tools for development and management in the public cloud for your organisation. Microsoft realised the importance of cloud integration as organisation continue to realise the cost benefits of running their database applications into the cloud but on a much larger